Follow this guide to install SentinelOne, Cove, DNSFilter, etc. Custom client fields can be used in scripts to install software with client-specific info (keys, tokens, etc.). This example installs:Documentation Index
Fetch the complete documentation index at: https://help.gorelo.io/llms.txt
Use this file to discover all available pages before exploring further.
- Cove
- SentinelOne
- BitDefender
- Webroot
- Cove
- SentinelOne
- BitDefender
- Webroot
Create the client custom field.
- Navigate to Settings > CRM > Custom Fields.
- Add custom field with the following details:
- Name: Cove Customer UID
- Variable: CoverCustomerUID
Populate the Cover Customer UID for each client.
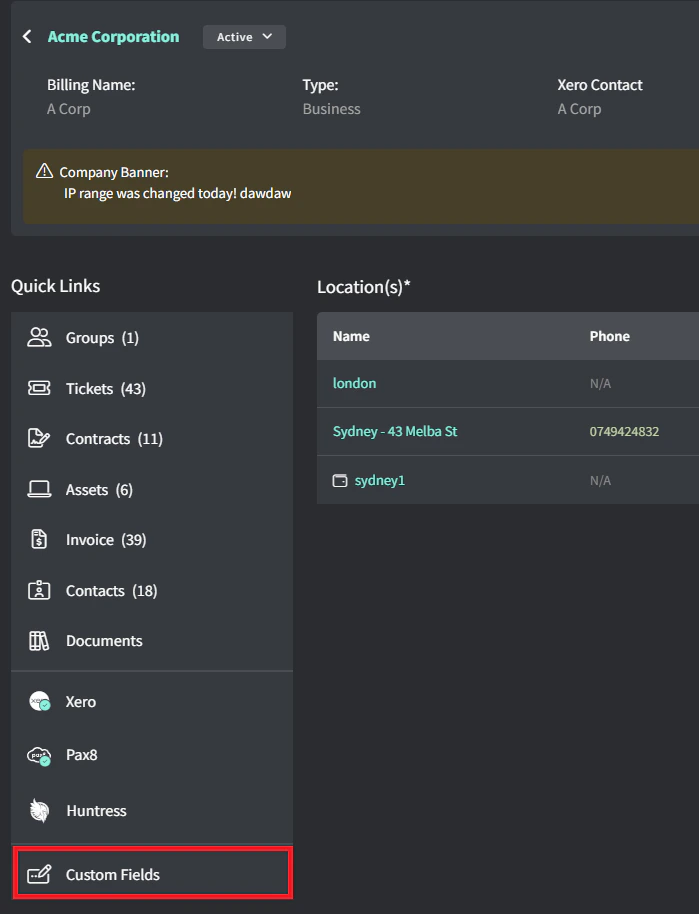
- Navigate to a specific client.
- Click Custom Fields.
- Edit Cove Customer UID.
- Enter the Customer UID retrieved from Cove.
Write the script.
- Navigate to Scripts.
- Create a script with the following details:
- Name: Install-Cove
- Content:
# ===== Configuration Variables =====
$CUSTOMERUID = $gorelo:client.CoveCustomerUID
$PROFILEID = "All-in" # Default retention policy
$PRODUCT = "0" # Profile ID (use "0" for no profile or a specific profile ID)
$DOWNLOADPATH = "C:\Windows\Temp"
# ===================================
$startTime = Get-Date
$INSTALL = "$DOWNLOADPATH\bm#$CUSTOMERUID#$PROFILEID#.exe"
# Download installer
try {
[Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls12
(New-Object System.Net.WebClient).DownloadFile("https://cdn.cloudbackup.management/maxdownloads/mxb-windows-x86_x64.exe", "$INSTALL")
} catch {
Write-Output "ERROR: Failed to download installer - $_"
exit 1
}
# Run installer
try {
Start-Process -FilePath $INSTALL -ArgumentList "-product-name `"$PRODUCT`"" -Wait -NoNewWindow
Start-Sleep -Seconds 5
} catch {
Write-Output "ERROR: Installation failed - $_"
exit 1
}
# Verify installation
$service = Get-Service -Name "Backup Service Controller" -ErrorAction SilentlyContinue
$process = Get-Process -Name "BackupFP" -ErrorAction SilentlyContinue
if ($service.Status -eq 'Running' -and $process) {
Write-Output "SUCCESS: Backup Service Controller is running and BackupFP process is active."
Write-Output "Installed for Customer UID: $CUSTOMERUID"
$exitCode = 0
} else {
Write-Output "WARNING: Backup Service Controller or BackupFP process is not running as expected."
Write-Output "Customer UID: $CUSTOMERUID"
# Check log for errors
$logDirectory = "C:\ProgramData\mxb\Backup Manager\logs\ClientTool"
if (Test-Path $logDirectory) {
$latestLog = Get-ChildItem -Path $logDirectory -Filter "*.log" | Sort-Object LastWriteTime -Descending | Select-Object -First 1
if ($latestLog) {
$errorLines = Get-Content -Path $latestLog.FullName | Where-Object { $_ -match '\[E\]' } | Select-Object -Last 3
if ($errorLines) {
Write-Output "Recent errors from log:"
$errorLines | ForEach-Object { Write-Output $_ }
}
}
}
$exitCode = 1
}
$endTime = Get-Date
Write-Output "Installation completed in $([math]::Round(($endTime - $startTime).TotalSeconds, 2)) seconds."
exit $exitCode
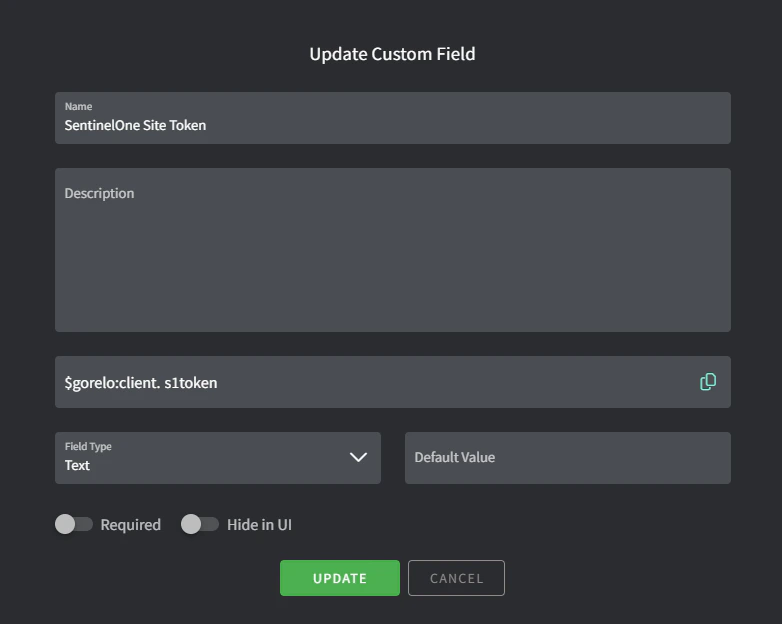
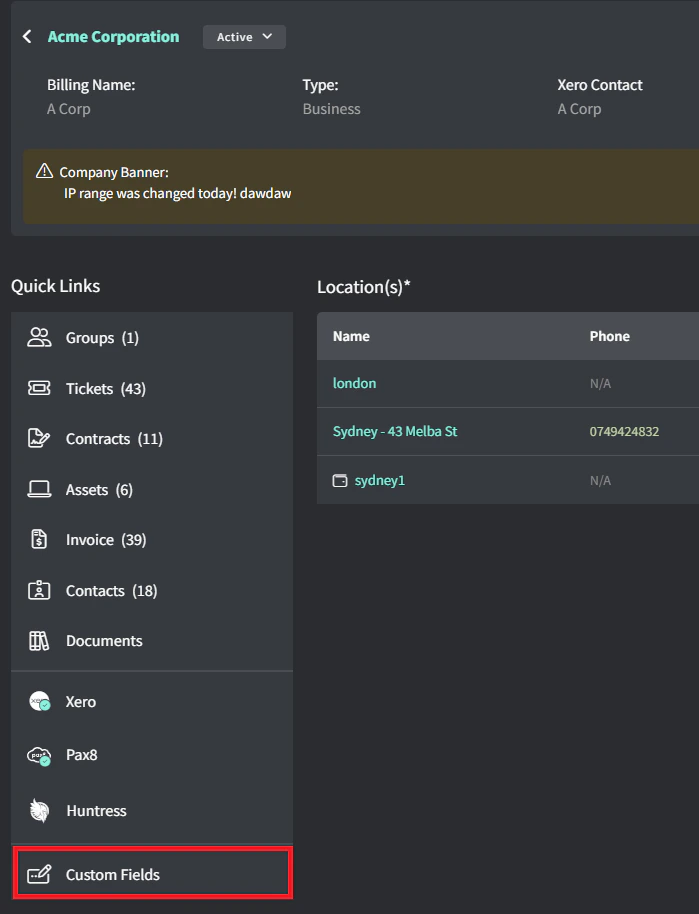
Create the client custom field.
- Navigate to Settings > CRM > Custom Fields:
- Add a custom field with the following details:
- Name: SentinelOne Site Token
- Variable: s1token
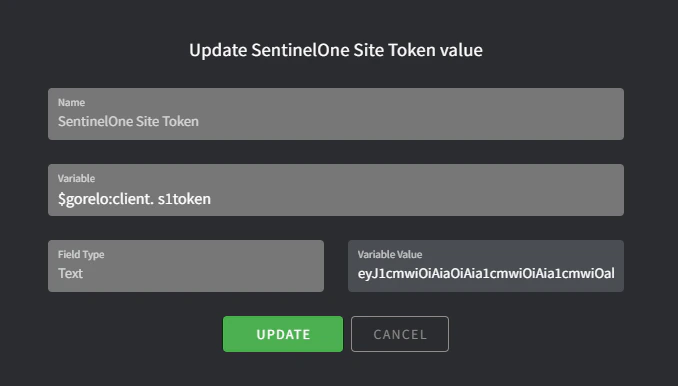
Populate the software token for each client.
- Navigate to a specific client
- Click Custom Fields.
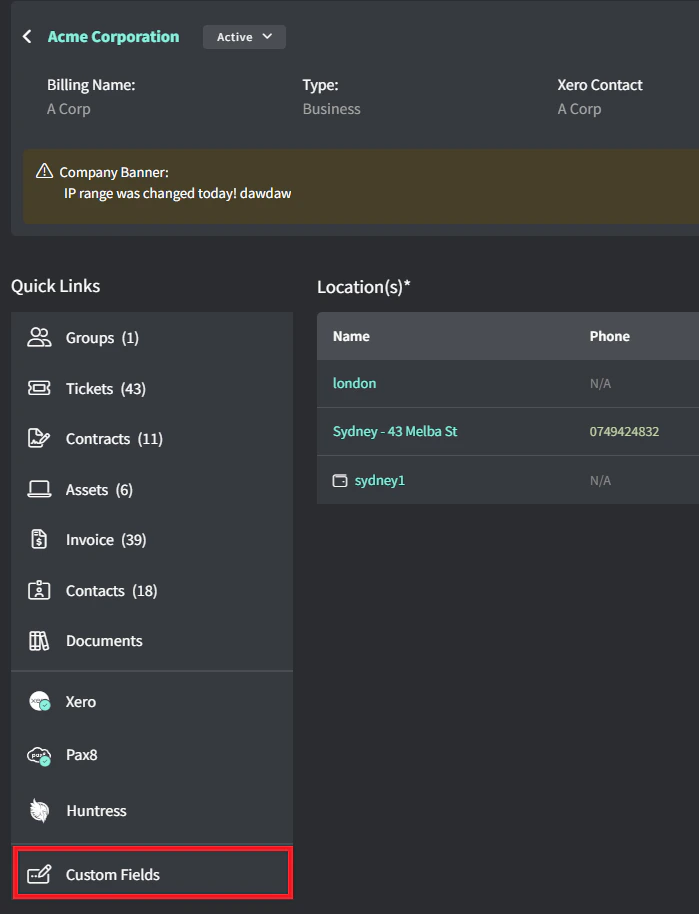
- Edit SentinelOne Site Token.
- Enter the Site Token retrieved from SentinelOne.
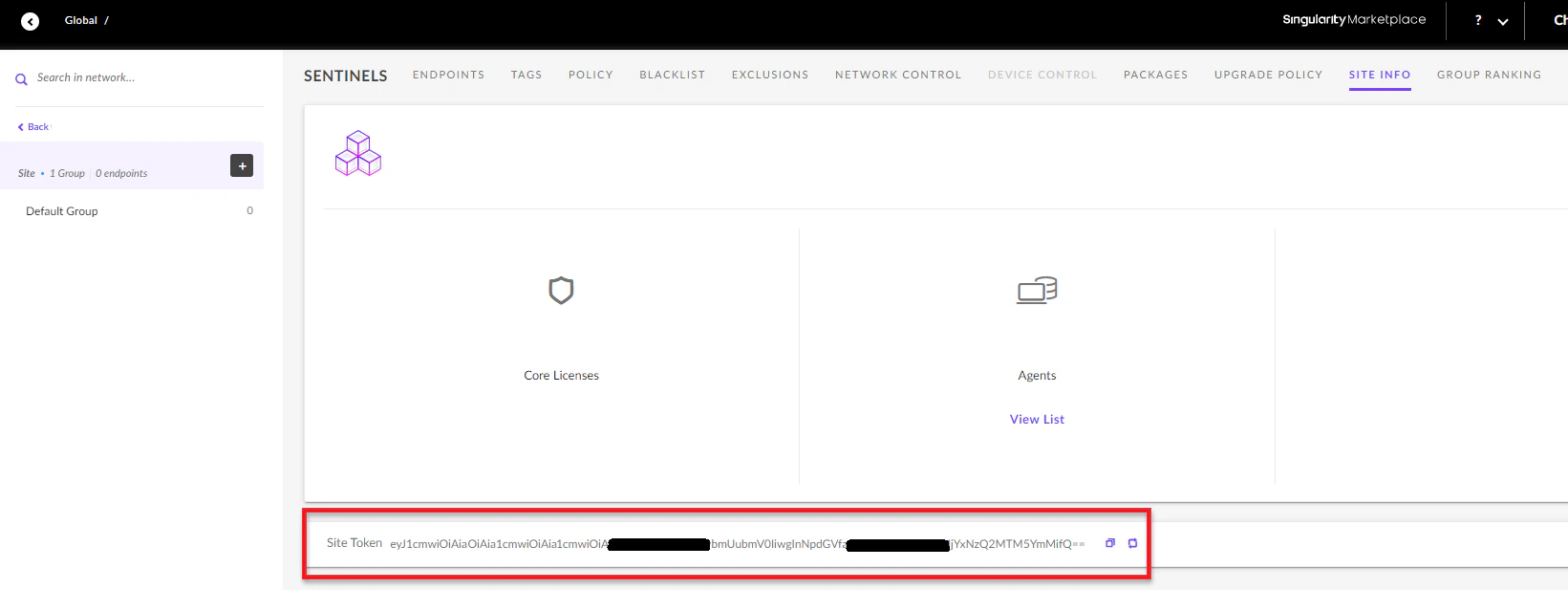
You can retrieve your SentinelOne Site Token from https://<DomainName>.sentinelone.net/dashboard. Navigate to a Site, then to the Site Info tab.
Create the installer file.
- Navigate to Settings > Asset > Files.
- Add a file with the following details:
- File: Upload the latest MSI installer
- Variable: S1Installer
Write the script.
- Navigate to Scripts.
- Create a script with the following details:
- Name: Install-SentineOne.
- Content:
#Silently install SentinelOne
if($gorelo:client.s1token){
$S1Service = get-service -Name 'Sentinel Agent' -ErrorAction SilentlyContinue
if($S1Service -eq $null){
msiexec /i $gorelo:file.S1Installer SITE_TOKEN=$gorelo:client.s1token /quiet /norestart
}
}
Deploy the script via a policy.
- Navigate to Policies.
- Edit an existing policy that covers the assets you want SentinelOne installed on.
- Add the Install-SentineOne script and set to repeat daily at your preferred time.
- Distribute the policy.
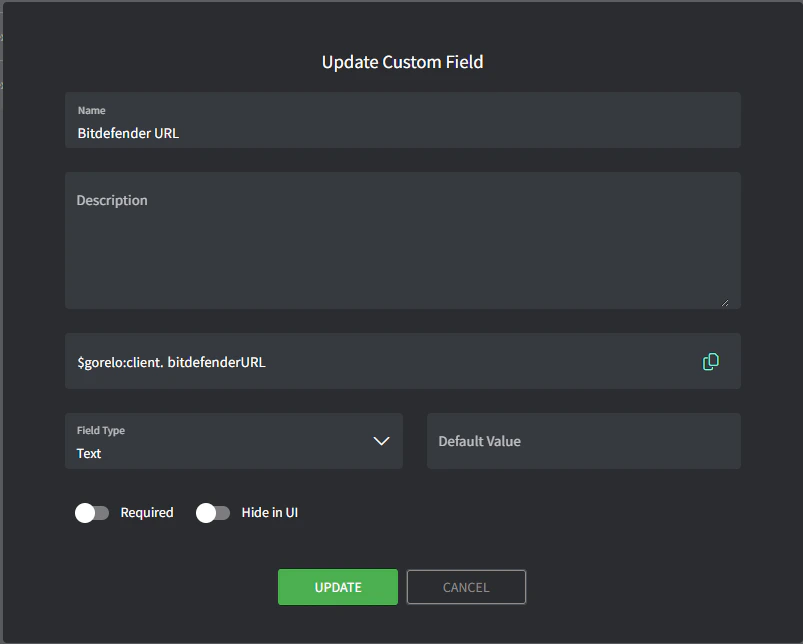
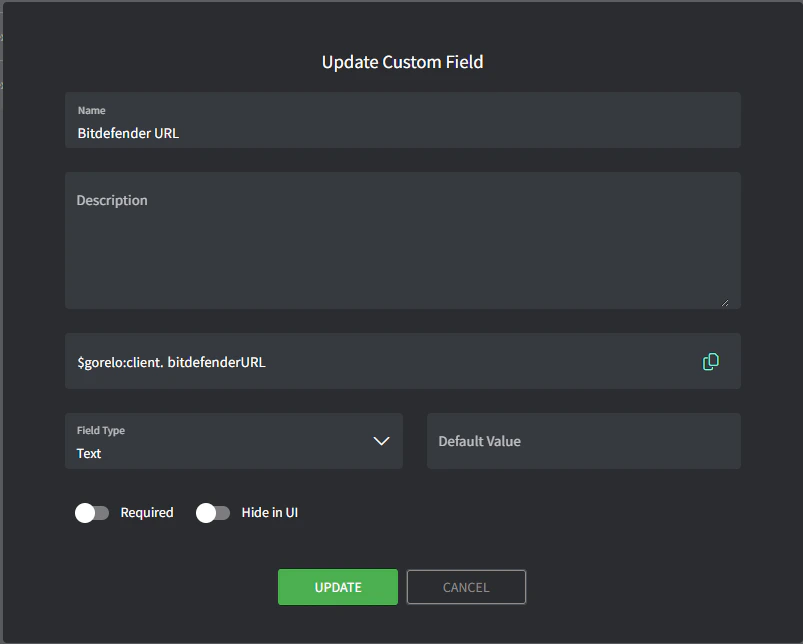
Create the client custom field.
- Navigate to Settings > CRM > Custom Fields.
- Add custom field with the following details:
- Name: Bitdefender URL
- Variable: bitdefenderURL
Populate the BitDefender URL for each client.
- Navigate to a specific client.
- Click Custom Fields.
- Edit Bitdefender URL.
- Enter the install exe URL retrieved from Bitdefender for each client.
 Bitdefender URL for the install exe should look like this (fake example):`htttps://cloudgz.gravityzone.bitdefender.com/Packages/BSTWIN/0/setupdownloader_[aHR0cHM6Ly9jbG91ZGdLWDawWVjcy5ncR5em9uZS5iaXRkZWZl3ddwawGfawdmRlci5jb20vUGFja2FnZXMvQlNUV0lOLzAvdkluc3RhbGxlci54bw-bGFuZz1lbi1VUw==].exe“
Bitdefender URL for the install exe should look like this (fake example):`htttps://cloudgz.gravityzone.bitdefender.com/Packages/BSTWIN/0/setupdownloader_[aHR0cHM6Ly9jbG91ZGdLWDawWVjcy5ncR5em9uZS5iaXRkZWZl3ddwawGfawdmRlci5jb20vUGFja2FnZXMvQlNUV0lOLzAvdkluc3RhbGxlci54bw-bGFuZz1lbi1VUw==].exe“
Write the script.
- Navigate to Scripts.
- Create a script with the following details:
- Name: Install-Bitdefender
- Content:
#$gorelo:client.bitdefenderURL
# Check if Bitdefender is already installed
if (Get-Service -Name "EPProtectedService" -ErrorAction SilentlyContinue) {
Write-Host "Bitdefender is already installed. Skipping installation."
exit 0
}
# Proceed with installation
$url = $gorelo:client.bitdefenderURL
$filename = Split-Path $url -Leaf
$installer = Join-Path $env:TEMP $filename
Write-Host "Downloading Bitdefender installer..."
(New-Object System.Net.WebClient).DownloadFile($url, $installer)
Write-Host "Installing Bitdefender..."
Start-Process -FilePath $installer -ArgumentList "/silent" -Wait
Remove-Item -LiteralPath $installer
# Verify installation
Start-Sleep -Seconds 10 # Give the service time to start
$service = Get-Service -Name "EPProtectedService" -ErrorAction SilentlyContinue
if ($service -and $service.Status -eq "Running") {
Write-Host "Installation successful! EPProtectedService is running."
exit 0
} else {
Write-Host "Installation may have failed. EPProtectedService not found or not running."
exit 1
}
Deploy the script via a policy.
- Navigate to Policies.
- Edit an existing policy that covers the assets you want Bitdefender installed on.
- Add the Install-Bitdefender script and set to repeat daily at your preferred time.
- Distribute the policy.
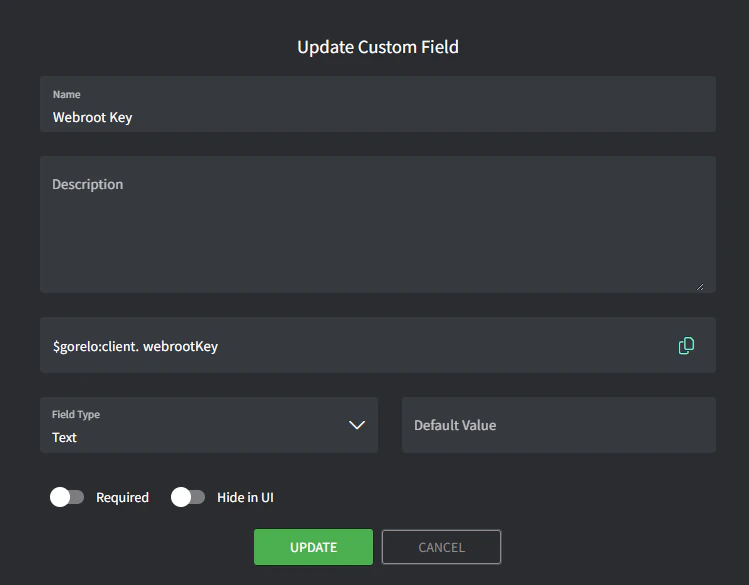
Create the client custom field.
- Navigate to Settings > CRM > Custom Fields.
- Add custom field with the following details:
- Name: Webroot Key
- Variable: webrootKey
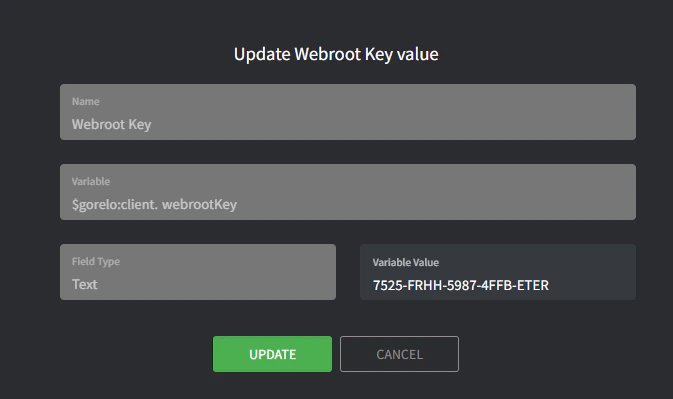
Populate the Webroot key for each client.
- Navigate to a specific client.
- Click Custom Fields.
- Edit Webroot Key.
- Enter the Webroot Key retrieved from Webroot.
Create the installer file.
- Navigate to Settings > Asset > Files.
- Add a file with the following details:
- File: Upload the latest MSI installer
- Variable: webrootInstaller
Create the script.
- Navigate to Scripts.
- Create a script with the following details:
- Name: Install-Webroot
- Content:
# Silently install Webroot
if($gorelo:client.webrootKey){
$WebrootService = Get-Service -Name 'WRSVC' -ErrorAction SilentlyContinue
if($WebrootService -eq $null){
msiexec /i $gorelo:file.webrootInstaller GUILIC=$gorelo:client.webrootKey CMDLINE=SME,quiet /qn /l*v install.log
}
}
Deploy the script via a policy
- Navigate to Policies.
- Edit an existing policy that covers the assets you want Webroot installed on.
- Add the Install-Webroot script and set to repeat daily at your preferred time.
- Distribute the policy.